- August 6, 2019
- Guillermo Gonzalez, Solutions Consultant

If you use any reputable PDF creation software, such as Foxit PhantomPDF or Adobe Acrobat, at some point, you may have seen this pop-up.
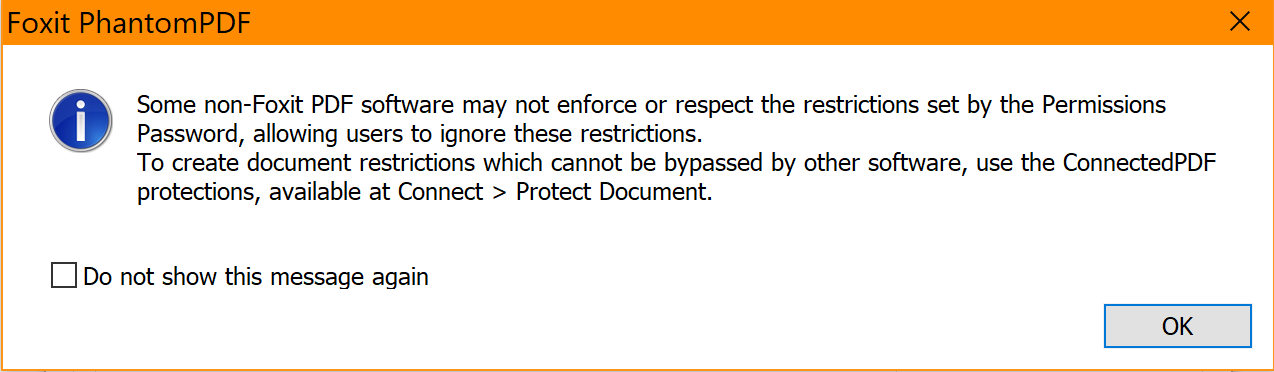
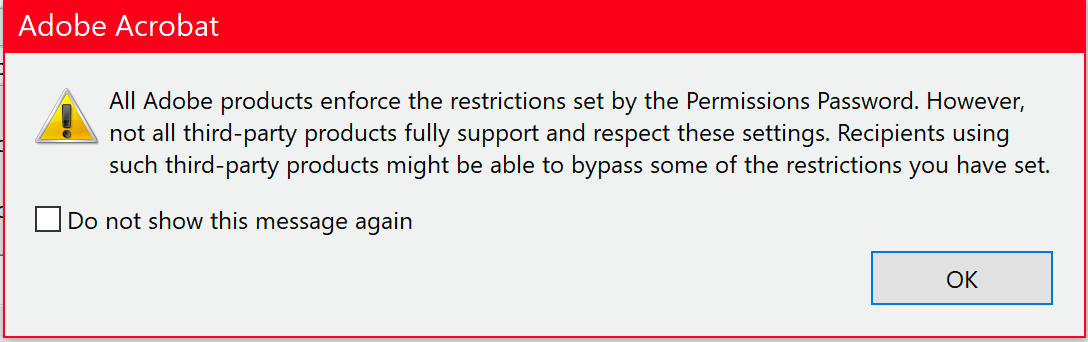
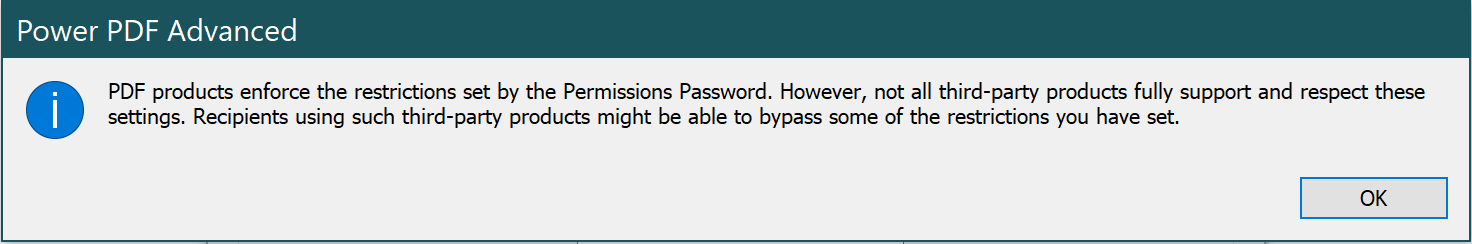
All PDF creation software that “follows the rules”—aka, adheres to ISO standards—displays it. But if you don’t remember it, you’re not alone. You probably just told the software not to show it anymore.
The only time you’re likely to see it again is if your company changes PDF software, such as making the move to standardize on some other PDF software like Foxit PhantomPDF, for example. In fact, that’s when we hear from customers who see it, are concerned about what it means, and want to know what they should do about it. So we’re here to help you with answers to those questions.
What this pop-up means
All reputable PDF software follows ISO standards, but there are a lot of software products out there that don’t. So, this pop-up is warning you to watch out if you or someone in your organization uses non-ISO compliant PDF software. Because if you do, there’s a chance that software could break your password restriction on PDF documents and share those documents with others.
This is a worst-case scenario, of course. While we at Foxit haven’t seen non-ISO PDF software completely decrypt a document, we have seen some products able to do things like change tags within the document.
So what should you do? The answer is to choose the right level of protection. Of course, to make that choice, you need to understand the three levels of document security and when to use them. And here’s a quick primer.
Know which level of document security you need
There are three different ways to protect PDF documents. They can be encrypted with a password, a Digital Certificate, and/or with Digital Rights Management Services (DRM) such as Azure Information Protected (AIP), also known as RMS, FileOpen or Foxit ConnectedPDF. Here’s how they stack up.
Password protection
The simplest way of protecting a document, password protection is a singular level of encryption. There’s no third party involved, no corporate verification. It’s simply the PDF generating encryption and allowing it to be decrypted. Anybody who has the password can open the document.
Password protection works well typically for small businesses and solopreneurs who are sending non-priority documents, and anybody who just needs the kind of basic document security it offers. When you need to go beyond basic password protection, your best course of action is to use certificate signatures and/or RMS.
Certificate Protection
If you’re a government agency, a bank, or an insurance company, or anyone sharing a document with sensitive data, you need to step up to third-party verification. This means you add a certificate signature, typically obtained through your IT administrator, to sign PDF files with a certificate-based digital ID.
Also known as digital signatures, certificate signatures usually are issued by a trusted third-party certificate authority. You can also use your Windows ID to create a third party verification via the Windows store.
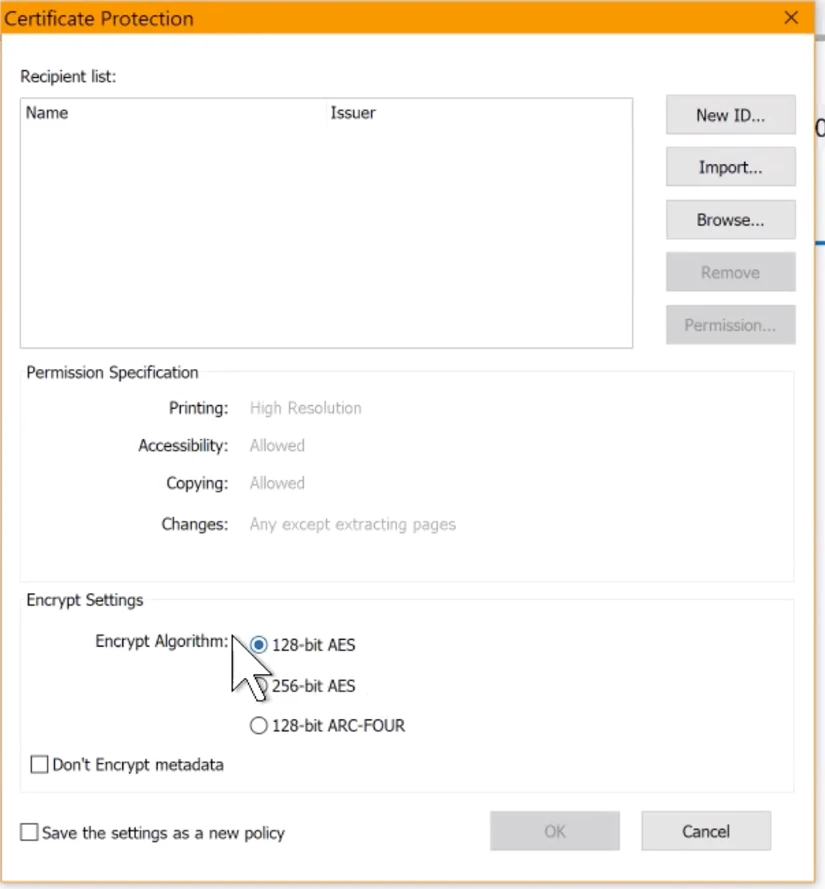
While this is considered sufficient document security by many, some choose to add standard encryption (username and password) to the document as well.
If you’ve added a username, password, and a certificate to your PDF document, when someone puts in the username and password, PhantomPDF pings the Windows ID or other third party associated with the certificate to verify that this person is who they say they are before allowing them to view the document.
Needless to say, Foxit supports third-party certification because we follow ISO standards.
Rights Management
The third level of PDF document security is Azure Information Protection (AIP) Also known as Microsoft Rights Management Services (RMS). This Microsoft Windows security tool provides ongoing data protection by enforcing data access policies automatically throughout an enterprise. For documents to be protected with RMS, the document’s application with must support RMS, which Foxit does.
RMS is set up by IT professionals at your company and enables you to set up active directories in which there is a hierarchy of people within it who have access to the documents that are being created and may be given different levels of access, depending upon department, group, or even individual.
So for instance, if you’re in the marketing department of Acme Software Corporation, you can have an RMS directory set up that says that Steve and his product department is allowed to view and make changes your documents, while Stephanie and her accounting department is allowed to view and print them only.
Corporate enterprise-level protection is tied to your corporate ID, meaning, when you log into the system using your ID, whether on site or remote, your company’s RMS activates automatically. You can access documents and SharePoint, and then apply and decrypt, using RMS directly from Phantom PDF.
Now that you know about different levels of document protection, the choice is yours
As you can see, while that pop-up referenced above is nothing to worry about, it is something to pay attention to, as it’s alerting you to the fact that when it comes to document protection, not all PDF software, nor all document protection, is created equally. Hopefully you’re better able now to pick which level makes the most sense for your needs.